The basic principles of Zk (Zero-Knowledge) proof technology cover critical cryptography and information security issues.
Introduction to Zero-Knowledge Proofs
In today’s digitally connected world, ensuring the privacy and security of data and transactions has become critically important. From financial services to healthcare, organizations across industries grapple with balancing openness with appropriate protection of sensitive information.
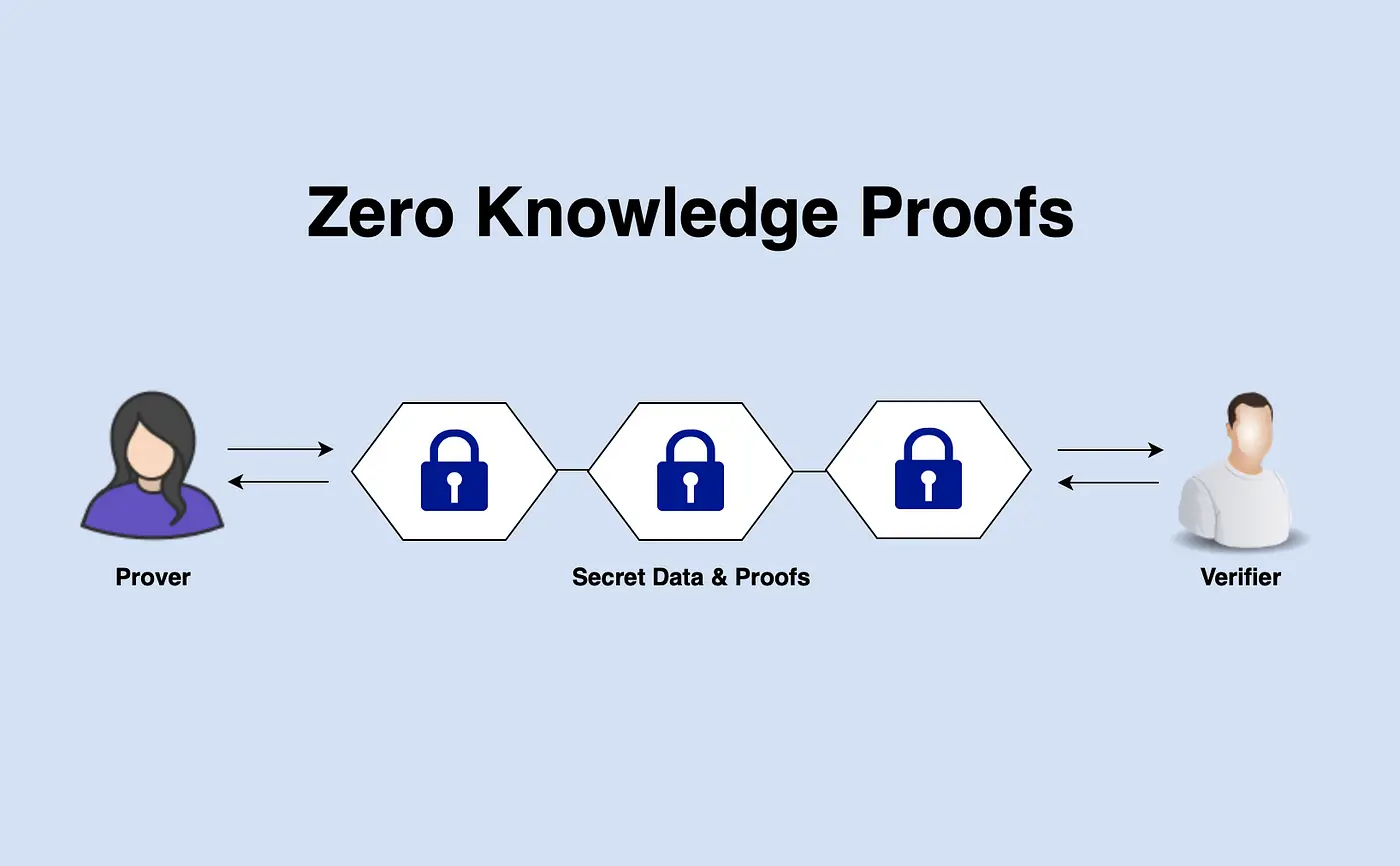
In this context, zero-knowledge proofs have emerged as a powerful cryptographic concept. Often abbreviated as ZKP or ZK proofs, these constructs enable one party to prove specific claims about data to another party without revealing the data itself.
Through sophisticated mathematical algorithms and protocols, ZK proofs allow verifying statements without compromising privacy. This unique feature addresses critical challenges around confidentiality that other methods cannot adequately solve.
As blockchain technology increasingly underpins digital infrastructure worldwide, ZK proofs play a pivotal role in providing privacy-preserving capabilities to distributed ledgers and applications built upon them. They represent an essential breakthrough for the future of privacy-centric systems and services.
This article seeks to demystify the basics of this advanced concept, examining the core principles that underlie how zero-knowledge proofs function. Understanding these foundations is critical to appreciating this groundbreaking cryptographic innovation’s advantages and appropriate use cases.
Let’s begin our discussion by further exploring these fundamental tenets of ZK technology.
Here are the basic principles of ZK (Zero-Knowledge) Proof Technology:
1. Security
Zk technology allows one party to prove something to another but does not disclose any information during the proving process. This is especially important in transactions where confidentiality must be maintained.
2. Verification
The Zero-Knowledge Proof (ZKP) mechanism is used to verify a claim. This confirms the transaction’s validity without revealing who the person making the transaction is.
3. Anonymity
Zk technology allows users to make transactions anonymously. This is especially important for situations where personally identifiable information must be protected.
4. Mathematical Foundations
Zk technology uses complex mathematical algorithms and cryptographic functions. These algorithms ensure that transactions are secure and verifiable.
5. Scalability
Different Zk technologies, such as Zk-SNARKs and Zk-STARKs, enable faster and scalable processing of transactions.
6. Deniability
Zk technology allows the person who carries out the transaction to deny this transaction later. This can be particularly important from a legal perspective.
7. Universality
The technology can be used in many areas, from financial transactions to identity verification, voting systems, and supply chain management.
8. Transparency and Auditability
Zk technology ensures that transactions remain transparent yet confidential. This is important for auditability and accountability.
These principles are critical to understanding how Zk technology works securely, confidentially, and effectively. These principles make the technology suitable for many industries and applications.
What are the Key Differences Between Zk-SNARKs and Zk-STARKs?
The critical differences between Zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) and Zk-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge) are based on several factors such as performance, security, transparency, and complexity.
Here are the main differences between these two technologies:
Security Model
Zk-SNARKs: Requires a trusted installation, which can pose a potential security risk.
Zk-STARKs: It does not require a reliable installation, thus providing a safer structure.
Transparency
Zk-SNARKs: Non-transparent and requires a “setup” phase.
Zk-STARKs: It is transparent and requires no hidden parameters or setup phases.
Performance and Scalability
Zk-SNARKs: Produces shorter proofs and is verified faster but may suffer from scalability issues for large data sets.
Zk-STARKs: Produces longer proofs but is more advantageous in terms of scalability.
Complexity and Efficiency
Zk-SNARKs: Requires less computing power, making it more efficient.
Zk-STARKs: Requires more computing power and storage space, making it more complex and costly.
Quantum Resistance
Zk-SNARKs: Risk of being breakable by quantum computers.
Zk-STARKs: Designed to be quantum resistant, making it more resistant to future quantum computer threats.
Scope of Application
Zk-SNARKs: Generally used more widely in blockchain and cryptocurrency projects.
Zk-STARKs: This may be more suitable for finance, supply chain, and other industries with significant data needs.
License and Cost
Zk-SNARKs: May have patent or licensing requirements.
Zk-STARKs: Generally open source and available without patent or licensing requirements.
Both technologies use the concept of zero-knowledge proof but offer different advantages and disadvantages for different application scenarios and requirements. So, which technology to use depends on your desired features and the application’s needs.
What is the Historical Development of Zero-Knowledge Protocols?
The historical development of Zero-Knowledge Proof (ZKP) and related protocols is essential in cryptography and information security.
Here are the main historical periods and developments on this subject:
1980s: Emergence of Fundamental Concepts
1985: The ZKP concept was introduced by Shafi Goldwasser, Silvio Micali, and Charles Rackoff in the article “The Knowledge Complexity of Interactive Proof Systems.”
1990s: First Implementations and Expansion
Early 1990s: The first practical ZKP systems were designed, and research in this area gained momentum.
1994: Interactive ZKP systems such as “Sigma Protocols” are developed.
2000s: Expanding Areas of Use
2000s: ZKP began to be used in various applications, such as authentication, digital payment systems, and secure data storage.
2009: With the emergence of Bitcoin, ZKP’s potential for blockchain technology began to be further explored.
2010s: Zk-SNARKs and Zk-STARKs
2013: Zerocoin and then Zerocash projects demonstrated how Zk-SNARKs could be used to provide privacy in cryptocurrencies.
2018: The Zk-STARKs concept was introduced as a more scalable and transparent ZKP solution.
The 2020s: Industrial Applications and Beyond
2020 and Beyond: ZKP has industrial applications in finance, healthcare, supply chain, etc.
Today: Work continues on quantum-resistant versions of ZKP and faster verification processes.
This historical process shows how ZKP and related protocols have evolved and where they are today. Although technology initially emerged as a theoretical concept, it has had many practical applications. Especially in the world of blockchain and cryptocurrency, ZKP plays a vital role in privacy and security.
Conclusion
In conclusion, zero-knowledge proofs have come a long way since their inception in the 1980s as a theoretical concept in cryptography. Over the past few decades, significant advancements have been made in developing practical implementations of ZKPs using techniques like Sigma Protocols and exploring use cases across domains like digital payments, authentication, and secure data storage.
The emergence of blockchain technology and cryptocurrencies in the 2000s significantly boosted the research and development of ZKP protocols. Innovations like Zerocoin and Zcash demonstrated how ZK-SNARKs could bring privacy to public blockchains, addressing a fundamental limitation. More recently, protocols like ZK-STARKs promise higher scalability and transparency.
Continued work is underway to strengthen these protocols against quantum computing threats. There is also work focusing on optimizations to reduce proof sizes and speed up verification times. This will be crucial for industrial deployments involving large datasets.
Zero-knowledge proofs have proven to be a highly transformative concept, moving from theory to widespread applications across finance, supply chains, healthcare, and more. As privacy and data security assume increasing importance globally, ZKPs and future variants are well-positioned to play a pivotal role in protecting sensitive information while enabling transparency and verification. The continued evolution of these protocols will be essential to watch.